Unlock Digital Transformation Without Forcing Equipment Replacement
Protect legacy operational technology against a new age of transport threats
Seamless Journeys Start With Secure OT Environments That Enable Transformation
Transport systems rely heavily on operational technology that powers everything from advanced sensors tracking passenger baggage to legacy industrial control systems running Windows XP that support critical railway signalling. Every link in your infrastructure must remain secure to maintain reliable operations, yet these same systems must also support digital transformation initiatives without forcing expensive replacement.
TXOne delivers transformation-ready security designed explicitly for transportation's unique challenge: protecting unpatchable legacy assets alongside modern systems while enabling secure connectivity for analytics, automation, and digital quality initiatives. Unlike detection platforms that document vulnerabilities without blocking threats, or isolation strategies that prevent transformation, TXOne provides purpose-built prevention that works where conventional security tools cannot—unlocking digital futures while honouring operational heritage.
RESEARCH REPORT
Legacy systems in transportation industrial environments
Our latest European research surveyed senior transportation professionals across six countries to reveal the critical protection gap. While detection platforms document thousands of CVEs on unpatchable systems, they cannot prevent the exploitation that 45% of organisations have already experienced.
Discover why 50% hesitate to implement conventional security due to operational concerns, how purpose-built approaches deliver 95% attack surface reduction without disruption, and what the 62% planning to invest reveals about market direction and competitive timing.
.png?width=486&height=690&name=mockup%20(1).png)
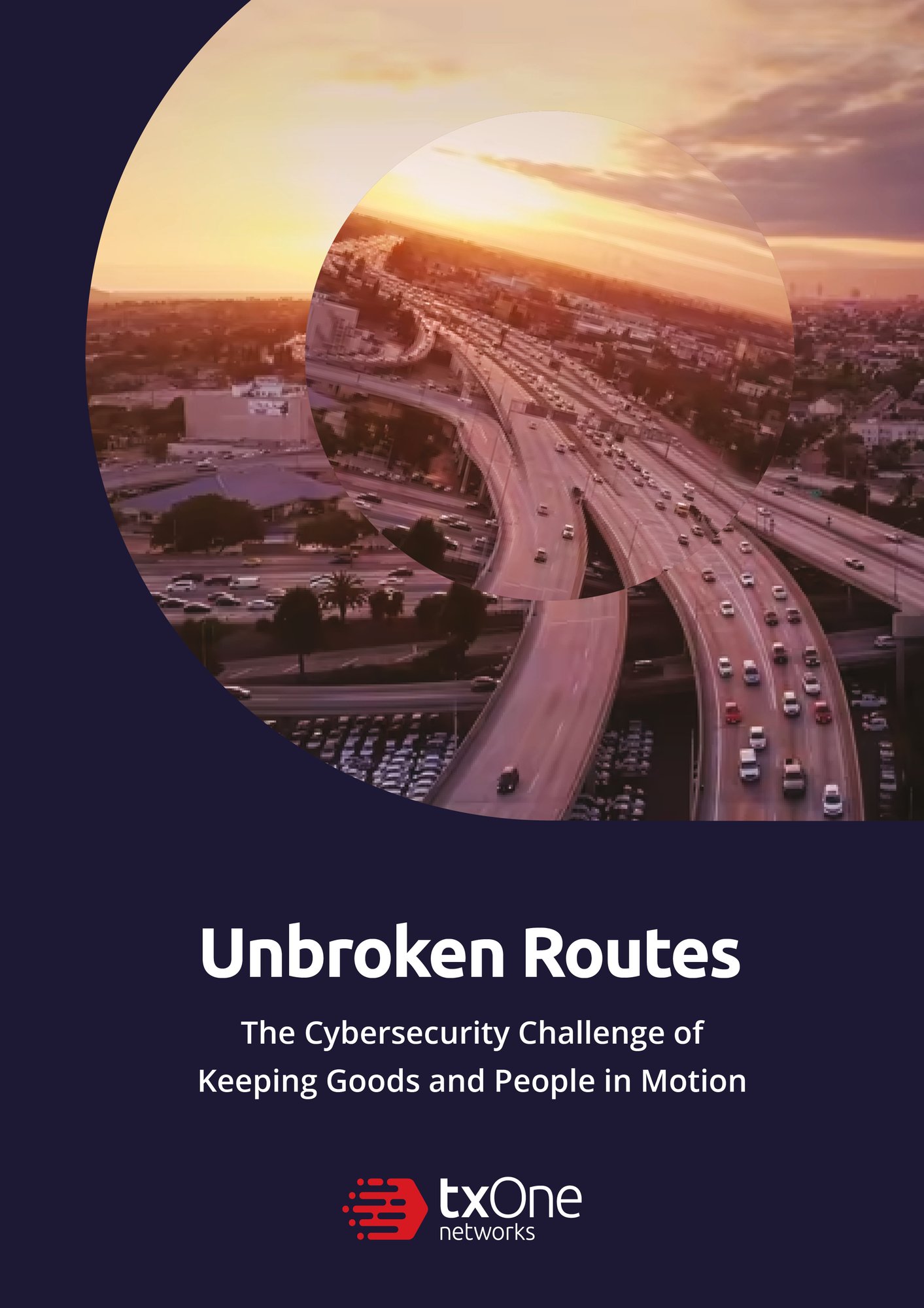
E-BOOK
Unbroken Routes
Robust OT Cybersecurity for Rail, Air, Marine, and Road Transportation
Explore real-world transportation sector breaches targeting legacy infrastructure, discover purpose-built defence strategies that enable transformation without forced replacement, and learn how organisations achieve 7-10 year secure life extension at 40-60% lower total cost.
TXOne: The OT Security Transformation Partner For Transport Operations
Transform While You Protect

Transform While You Protect
Secure unpatchable Windows XP, Windows 2000, and legacy industrial systems while unlocking budget and capability for digital transformation initiatives. Achieve 7-10 year strategic life extension at 40-60% lower total cost than forced replacement, redirecting $2-5M per major system from forced upgrades to analytics, automation, and digital quality programmes that create competitive advantage.

Unlock Digital Futures, Not Just Prevent Attacks
Virtual patching enables secure connectivity for data analytics and automation on systems that were forced into isolation by legacy systems, leaving them disconnected from transformation initiatives. Purpose-built prevention turns legacy systems from strategic liabilities into transformation enablers, addressing the operational concerns that make 50% of organisations hesitate to implement conventional security.

Transformation-Ready Compliance
Align with NIS2 directive and industry standards through demonstrated prevention capabilities that satisfy regulatory requirements while establishing security architecture supporting future digital initiatives. Unlike detection-only approaches that document vulnerabilities without enabling transformation, or isolation strategies that block connectivity, TXOne delivers compliance without constraining strategic flexibility.
TXOne OT-Native All-Terrain Solutions
Zero-Trust Security Inspection
TXOne Element delivers rapid, installation-free validation designed specifically for air-gapped environments and legacy systems where conventional security creates operational risk. Enable secure transformation on systems that are forced replacement strategies, targeted for disposal.
- Transformation-ready asset validation: Validate Windows XP, legacy PLCs, and decades-old systems where software installation cannot occur, enabling secure connectivity for digital initiatives without forced replacement.
- Secure transformation pathways: AES-256 encrypted storage ensures only validated files reach air-gapped legacy systems, enabling controlled connectivity for analytics and automation.
- Protection for transformation-constrained systems: Safe Port media sanitiser identifies and eliminates malware before reaching legacy systems that cannot defend themselves, enabling secure data transfer for digital initiatives.
- Complete legacy infrastructure visibility: Identify every asset, including unpatchable systems, from a unified dashboard, enabling strategic transformation planning with full asset knowledge.
Endpoint protection for legacy and modern OT assets
Stellar Endpoint Protection secures Windows XP, Windows 2000, and legacy industrial controllers without requiring software installation, system modification, or validation disruption that blocks transformation initiatives. Enable 7-10 year strategic life extension while supporting secure connectivity for digital programmes.
- Transformation enablement on legacy infrastructure: Protect network drives and removable media without installing agents on fragile legacy systems, enabling secure data flow for analytics and automation initiatives.
- Real-time protection without update requirements: Operational behaviour anomaly detection identifies unusual patterns on legacy systems where signature updates cannot be applied, enabling continuous protection as transformation initiatives evolve.
- Validated process protection: Application lockdown protects approved processes on legacy systems, ensuring transformation initiatives build on proven operational workflows rather than disrupting them.
- Secure transformation connectivity: USB vector control enables controlled connectivity for legacy systems while preventing unauthorised access, supporting digital initiatives without creating vulnerabilities.
Trusted OT network protection
TXOne EdgeIPS delivers network-layer protection with virtual patching designed specifically for legacy industrial protocols, enabling secure connectivity for transformation initiatives on systems that cannot accept conventional patches or agent installation.
- Virtual patching enabling transformation: Block CVE exploitation on Windows XP and legacy systems through network-based protection while enabling secure connectivity for data analytics, automation, and digital quality initiatives.
- Legacy protocol support for transformation: Deep understanding of legacy Modbus RTU, proprietary SCADA protocols, and industrial communications enables secure data flow for analytics and automation without forcing replacement.
- Transformation-ready network architecture: Micro-segmentation without agent requirements reduces attack surface while enabling controlled connectivity for digital initiatives, supporting transformation without operational conflicts.
- Strategic transformation planning: Vulnerability mapping for end-of-life systems provides early warning while enabling strategic life extension planning, supporting transformation timelines without crisis-driven replacement.

WEBINAR
On the Right Track: Cybersecurity in Transportation
Join our experts for an insightful webinar that discusses the challenges facing transport operators and strategies you can adopt to protect your OT assets.
Key Takeaways:
- Sector insights and an exploration into securing diverse and layered transportation environments.
- The key regulations impacting the industry and how they shape security protocols.
- Innovative approaches to protect critical infrastructure and assets.
Other Resources

Future Cybersecurity Threats in Ports: Protecting Global Trade from Rising Maritime Risks
- maritime industry
- ransomware
- supply chain security

Railroads at Risk of Remote Hijacking
- critical infrastructure
- threat research
- transportation industry

CBTC: Vulnerabilities of Communication-Based Train Control Architecture
- cyber attacks
- threat research
- transportation industry

Railway Cybersecurity: a Look at Potential Threats
- cyber attacks
- OT zero trust
- railway industry
- threat research

Anatomy of Intelligent Infrastructure in Railway Stations
- transportation industry
- threat research
Keep passengers safe and your transport network on the move.
Discover how purpose-built prevention unlocks digital futures while protecting operational heritage.